This post explains how small to mid-sized contractors can implement robust identity authentication for IoT and embedded devices to satisfy FAR 52.204-21 and the CMMC 2.0 Level 1 control IA.L1-B.1.VI, concentrating on actionable steps, technical choices, real-world examples, and the artifacts auditors expect to see under the "Compliance Framework" practice.
Start with an inventory and risk-driven design
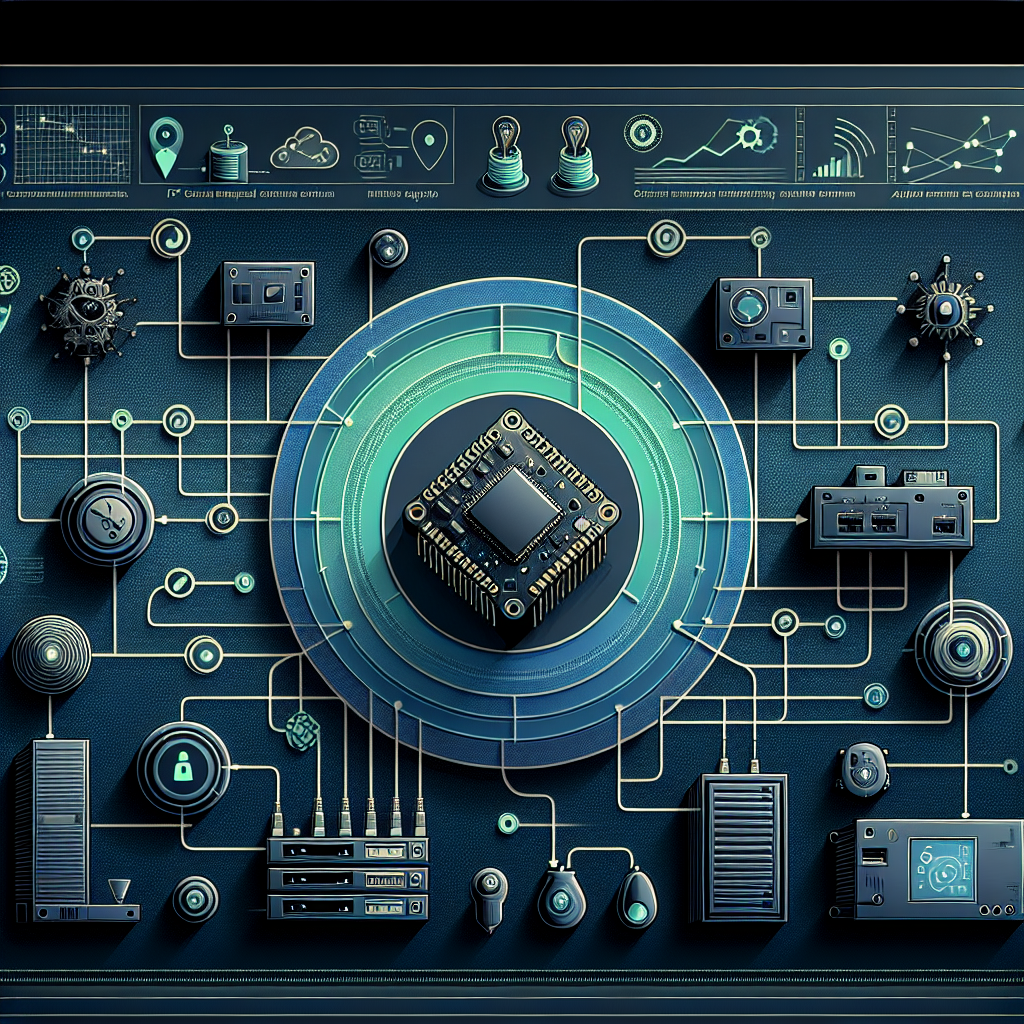
Begin by building an authoritative inventory of all embedded and IoT devices (manufacturer, model, firmware, physical location, network connectivity, function, and whether they process or transmit Controlled Unclassified Information/contractor information). Classify devices by risk (remote access, Internet-exposed, USB/update capability) and group them into trust zones. For Compliance Framework evidence, produce a spreadsheet and supporting network diagrams showing device classes, trust boundaries, and which devices will require cryptographic identities versus simple authenticated API keys.
Choose device identity methods appropriate to constraints
Pick identity/authentication mechanisms based on device capability: for moderately capable devices (Linux, RTOS, gateways) use X.509 certificates and mutual TLS (mTLS) with TLS 1.2+/1.3; for constrained devices consider DTLS with raw public keys or OSCORE/COSE for CoAP; for lightweight telemetry where TLS is impractical, use short-lived JSON Web Tokens (JWT) issued via a gateway and signed with ECDSA. Always prefer hardware-backed keys where available: TPM 2.0, Secure Element (e.g., ATECC608A), or ARM TrustZone. Recommended cryptography: ECDSA P-256 or RSA-2048 minimum, TLS 1.2+ with AEAD ciphers (AES-GCM or ChaCha20-Poly1305), and disable legacy ciphers and versions (TLS 1.0/1.1, static RSA key exchange).
Provisioning, lifecycle management, and key management
Design a provisioning and lifecycle process: unique identities must be provisioned (not shared or hard-coded default passwords). Options include factory provisioning (each device provisioned with a unique cert/key and device ID), Just-in-Time (JIT) provisioning with a one-time enrollment token, or cloud-managed enrollment (AWS IoT, Azure IoT Hub, or a private PKI) that issues certificates on first connect. Implement automated certificate rotation (consider 90–365 day lifetimes for device certs depending on operational constraints), a clear revocation method (CRL/OCSP or cloud-side deny lists), and documented procedures for device replacement, re-provisioning, and secure decommissioning. For evidence, keep enrollment logs, CA issuance records, and key rotation schedules.
Network segmentation, gateway patterns, and small-business examples
Segment device networks from corporate and developer networks using VLANs, firewalls, and NAC. For a small manufacturer with 200 production sensors and a few field gateways, an effective pattern is: devices -> local gateway (edge) that enforces mTLS and message validation -> cloud IoT broker. Gateways can handle constrained-device authentication (device pre-shared key or local secure element) and present a hardened identity to the cloud. Example: a small HVAC controls contractor uses ATECC608A secure elements soldered on PCBs to store device private keys, gateways running mTLS terminate to AWS IoT Core with device certificates, and an internal PKI issues short-lived certs for gateways. This minimizes exposure if a single device is compromised because the gateway enforces authorization and telemetry rate limits.
Logging, monitoring, and compliance artifacts
Implement tamper-evident logs and monitoring: collect device authentication events (successful/failed authentication, certificate issuance/revocation, firmware-update signatures), and maintain central logs for at least the period required by your contract. For IA.L1-B.1.VI evidence, provide: device inventory, CA certificate chain, enrollment logs, sample TLS handshake captures showing client certs, revocation/deny list snapshots, architecture diagrams, and procedures (provisioning, revocation, incident response). Tools that help small businesses include lightweight syslog collectors, cloud IoT monitoring dashboards, and automated certificate management (e.g., certmanger-style agents or cloud CA APIs).
Risks of not implementing strong device authentication
Failing to implement unique, verifiable identities permits device impersonation, unauthorized data access, lateral movement into contractor networks, and tampering with telemetry or commands — all of which can expose Controlled Unclassified Information, disrupt mission systems, and trigger contract noncompliance under FAR 52.204-21. Real-world consequences include data exfiltration, expensive incident response, contract penalties, and loss of DoD trust. A single compromised device with shared credentials can allow attackers to pivot to vendor portals or firmware update servers if authentication is weak or non-unique.
Practical tips and best practices for small businesses
Actionable checklist: never ship devices with default credentials; require unique device identity at manufacture or first boot; prefer hardware-backed keys; centralize certificate/key lifecycle with documented rotation and revocation; use mTLS or equivalent mutual authentication; enforce least-privilege network segmentation; sign firmware updates and verify signatures on-device before installation; maintain enrollment and revocation logs as compliance artifacts. Cost-effective approaches for small shops include using cloud IoT identity services (AWS IoT Core, Azure IoT Hub) for certificate management or procuring secure elements for mass-produced units. Consider a phased rollout: pilot 10–20 devices with full mTLS and hardware keys, validate provisioning, then scale.
In summary, meeting FAR 52.204-21 and CMMC IA.L1-B.1.VI for IoT/embedded devices requires a repeatable, documented approach: inventory and classify devices, choose appropriate cryptographic identity mechanisms, implement secure provisioning and lifecycle management, segment networks, and collect the artifacts auditors will ask for. For small businesses the right balance is adopting pragmatic hardware-backed identities where possible, leveraging cloud-managed PKI or IoT platforms to reduce operational burden, and documenting every step—this reduces risk, satisfies compliance, and keeps your contracts secure.